 Section
Navigation
Section
Navigation
2. Social Dimension
2.1.
Scope of the Internet
2.2 Business
to Business Successes
2.3 Business
to Customer Successes
2.4 History
of the Internet
2.5 Differences:
India and China
2.6 eBusiness Law
2.7
eBusiness Tax
2.8 Cyber Crime
2.9
Cyber Wars
2.10 The Death of Print
2.11 Intellectual Property Issues
2.12 Online Privacy
2.13
Governance of the Internet
2.14 Welfare Issues
2.15 Internet Prospects
 2.12
Online Privacy
2.12
Online Privacy
Personal information is not merely a person's name, address and Social Security number, but his or her shopping habits, driving record, medical diagnoses, work history, credit score, political affiliation, vacations, social contacts, educational record and more. The right to privacy refers to control over this personal data: who can acquire, keep, access and process this information.
Privacy is an inherent human right, namely to be free of surveillance from other individuals, organizations and/or the state.
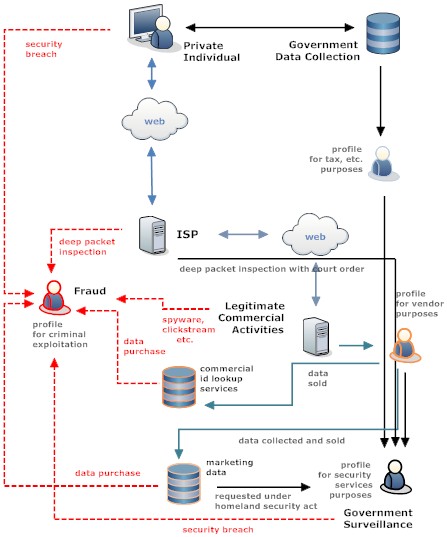
To the disquiet of many {1} {15} {20} {21} {22} {26} {27} {49}, privacy is under increased threat today, with the Internet greatly facilitating the collection, storage and analysis of personal data. {51} {52} {53} {54} {58} {71} Realists of the Mortengau school will see this as the usual devil's bargain, the price paid by companies and individuals for wider access to information.
1. Federal, state and local governments collect personal information in pursuance of their duties, and that information is accessible to law enforcement agencies through several pieces of legislation: Communications Assistance for Law Enforcement Act, the USA Patriot Act and the Homeland Security Act, in many instances without judicial oversight. {2} {4} {5} {25} {64} Similar information is protected in Europe under more stringent Data Protection Acts, but can be accessed by tax and law enforcement officers and/or for reasons of 'state security'. {3} {6}
2. Similar information, often very detailed, noting interests, social preferences and purchase histories is routinely collected by:
a. Shopping carts: merchant must keep
this information safe, but may use it for marketing purposes (as does Amazon in making
book suggestions) or sell it on to third parties.
b. Search engines: government
requests that browsing information be stored by ISPs and made available to courts
and law enforcement agencies has met with mixed success. {7} {53} {54}
c. Spyware:
inadvertently downloaded, such programs can collect passwords, security codes, browsing
histories, etc.
d. Social media: personal data can be sold or made available
to third parties, {8} {23} usually advertisers but potentially to criminal elements.
e. Cookies and supercookies that track and profile Internet users. Some can be
avoided by setting the browser security controls higher, but five new types evade
such controls and are difficult to remove. {9}
f. Web bugs that track advertising
campaigns. {52}
g. Advertising networks that track individuals across the Internet
(e.g. Clickstream) can sell that information to advertisers. {10}
h Service suppliers
like Google collect information, either for their own use or to be sold for marketing
purposes.
i. Forms: email addresses and profiles collected to receive some report
or benefit can be sold on, or linked to advertising networks.
j. Deep Packet
Inspection: networking technology that ISPs install to monitor customers' data {11}
{12}: used to target advertising and terrorist activity. {25} {54}
k. Server traffic
logs: routinely saved by ISPs and therefore available for analysis: who visited what
pages when, etc.
l. Internet Payment Service Providers: detailed customer information
(often including bank accounts) becomes available to third parties if security is
breached (or some parts sold on).
m. Trusted computing environments: restrict
viewing of sensitive material but also store user information for identification purposes.
{13}.
n. Email addressing harvesting software (e.g. Atomic Email Hunter) that
collects email addresses, owner's names and interests for subsequent email marketing.
{14}
o. Companies providing a background check on individuals (e.g. PeopleSearch
and WhoWhere) {16}
Such information becomes more valuable when combined. A travel company offering snorkeling holidays in Thailand would be interested in subscribers to a diving magazine who also browsed web pages on holidays in the country. The security services would be failing in their duties if they did not look more closely at someone in email correspondence with animal liberation groups who started researching bomb-making equipment on the Internet.
Privacy Legislation
Broadly speaking, privacy is enshrined by legislation in Europe, but left for individuals to sue for violations in the USA. {5} Nonetheless, most countries have extensive legislation in place. {17} {18} {19} {24} {41} {42}
USA:
Felony: to use a computer to commit fraud, to maliciously
access a computer without authorization, and to damage, copy, or remove files.
Misdemeanor: to use a computer to examine private files without authorization.
Computer Fraud and Abuse Act (CFAA): 1986
Felony: unauthorized access
to a Federal computer system with the intent to steal or commit fraud or inflict malicious
damage.
Misdemeanor: to traffic in passwords.
Electronic Communications Privacy Act: 1986
Electronic communications are private. Unauthorized access to and disclosure of private communications is unlawful.
Communications Assistance for Law Enforcement Act (CALEA) : 1994
Law enforcement and intelligence agencies can conduct electronic surveillance.
Freedom of Information Act: 1996
Guaranteed access to data held by the state. Nine exemptions apply, including state security, commercially sensitive information, medical records, etc.
Communications Decency Act (CDA): 1996 (Overturned in 1997)
Felony: to transmit obscene or offensive material over the Internet.
Web Copyright Law: 1997
Infringement of copyright-protected material valued at least $1000 can be prosecuted, even if there is no profit from the crime. Penalties are heavy.
Child Online Protection Act (COPA): 1998
Federal crime: to transmit material that is harmful to children over the Internet for commercial purposes.
Digital Millennium Copyright Act: 1998
New rules, safeguards and penalties for downloading, sharing, and viewing copyrighted material online.
Gramm-Leach-Bliley Act: 1999
Authorized widespread sharing of personal information by financial institutions such as banks, insurers, and investment companies.
Safety and Freedom through Encryption (SAFE) Act: 2000
Relaxed US export controls on encryption.
Patriot Act: 2001
Drastically increased federal police investigatory powers, including the right to intercept email and track Internet usage.
Homeland Security Act: 2002
Centralized federal security functions to meet post-cold war threats and challenges.
Intelligence Reform and Terrorism Prevention Act: 2004
Promoted a culture of information sharing among intelligence agencies and federal departments. Set up a five-member Privacy and Civil Liberties Oversight Board to protect privacy and civil liberties.
Internet Spy Act: 2011
ISPs must retain data on customer use for twelve months.
Cyber Intelligence Sharing and Protection Act 2012
Cyber threat information can be shared between the U.S. government departments and security companies.
EUROPE:
Article 8 of the European Convention on Human Rights
Most European countries adhere to the above which declares:
Everyone has the right to respect for his private and family life, his home and his correspondence. Exceptions apply: for reasons of: national security, public safety, crime, disorder, public health, morals, threatened rights and freedoms of others.
Individual countries retain their own legislation, however: France has a law recognizing the right to privacy, but the UK does not.
Freedom of Information Acts
Guaranteed access to data held by the state. Passed by most countries, but data can be held back for state security reasons or simply delayed by 'staff shortages'.
Does Privacy Matter?
For many of today's Internet citizens, privacy does not matter. They take the view of a 2008 NYT article {30} that privacy is dead, which is a 'good thing' because everyone can now spy on everyone else and stop 'bad guys'. People (especially people in 'terrorist' countries) need to get accustomed to having their activities recorded and judged by concerned fellow citizens. {31}
Authorities indeed often argue for increased surveillance by saying 'if you've done nothing wrong, then you've got nothing to worry about.'
On practical grounds (i.e. leaving aside a country's Constitution, {63} the ethical issues and experience of life in a police state), the counter-arguments are:
1. Without some privacy, individuals and companies cannot maintain
competitive advantage, which negates the capitalist system. {47} {66}
{70}
2. Subsequent anonymity is needed by whistle blowers and crime witnesses
if they are not to face uncertain futures, and be less willing to testify.
{41} {42}
3. Democracy is endangered if citizens cannot privately discuss matters
of common concern. {51} {52} {53} Surveillance can pass into harassment,
and then into the suppression of inconvenient views or evidence.
In particular:
a. Once collected, {48} {49} {50} {51} {52} {53} {54} information is
not easily removed. No security system is entirely safe, and information
becomes accessible to private interest groups, foreign powers or rogue
elements of government. {44}
b. Diverse opinions, some unwelcome to the state {36 {37} {38}, are
a feature of free societies, and free societies are generally the more
prosperous. {56}{62}
c. The 'nothing to fear' argument operates largely in one direction,
and governments often seem more concerned to 'shoot the messenger' than
correct the injustices exposed. {43} {65} The extent of illegal spying
by western governments on their own citizens is now being disclosed,
with the whistleblower being denounced as a 'traitor' by mainstream
media channels ostensibly charged with 'speaking truth to power'. {69}
Moreover, even as illegal surveillance is being extended, more documents
(tens of millions yearly) are being witheld from citizens whom governments
claim to answer to. {76}
d. Security matters are indeed not properly balanced by accountability
to citizens — who are supposedly served by government officials,
pay their salaries {38} and are seen abroad as supporting their policies.
{55} {38} That governments do routinely misbehave and cover up while
prosecuting citizens for lessor crimes {32} {33} {34} {35} {36} {37}
argues double standards, {68} and fuels attitudes that range from distrust
to conspiracy theories. {45} {46} {58-61} Citizens become disaffected
with government, which is then deprived of the trust, support and cooperation
it needs to function effectively.
e. US data collection passes into commercial and industrial espionage,
{74} which is damaging the reputation and prospects of all US IT companies.
{69} {73}
f. Data can and is used to blackmail individuals at all levels of government,
military and corporate life. {72}
g. NSA activities go beyond surveillance: bank accounts, commercially
sensitive information, computers, networks and software can be taken
over and altered by the intelligence services without judicial oversight,
or indeed legal disclosure for one year. {75}
Online Privacy Protection
Beyond not providing more information than specifically required, privacy is improved by:
1. Appointing a chief privacy officer to stay abreast of legislation
and ensure the company meets requirements.
2. Surfing anonymously through systems like anonymizer, etc.
3. Encrypting all sensitive material with disk encryption software.
4. Blocking and removing spyware with superantispyware, etc.
5. Securing emails with hushmail, PGP, etc.
6. Erasing data on discarded hard disks with programs like secure erase,
etc.
7. Removing cookies with browser controls and/or with programs like
ccleaner, etc.
8. Blocking pop-ups with browser controls or software.
9. Using software provided by companies not implicated in government
surveillance, if such exist. {67}
10. Moving to open-source, self-modified software.
11. Avoiding cloud storage of sensitive information, particularly when
servers are located in Britain or America.
12. Keep up to date with the more investigative and independent journalism
on NSA and GCHQ. {75}
 Questions
Questions
1.
What are the main threats to personal privacy on the Internet, and how serious are
they?
2. Outline the legislation relating to online privacy in the USA.
3. How does Europe generally treat online privacy?
4. Suggest practical measures
to improve online privacy.
5. Do you think online privacy is an an important
matter? Give the arguments for and against.
 Sources
and Further Reading
Sources
and Further Reading
1. Online trust and perceived utility for consumers
of web privacy statements by Mark Gazaleh. SkyDrive.
July 2010.
2. News You Need To Know About Information Security Laws. About.Com.
Short but useful listing of news items.
3. Security legislation. Watson
Hall. Links to acts applying to UK, Europe and to some extent the
USA.
4. Internet Privacy. Wikipedia.
Extensive and well-researched article. See Reference 49.
5. 'La difference' is stark in EU, US privacy laws by Bob Sullivan.
Privacy
Lost. Pros and cons of European approaches.
6. Data Protection Act 1998. UK
Government. Provisions of the law: other European countries have
similar exemptions.
7. DOJ Renews Push For Mandatory ISP Data Retention by Karl Bode.
Broadband
reports. January 2011.
8. How Online Tracking Companies Know Most of What You Do Online
(and What Social Networks Are Doing to Help Them) by Peter Eckersley.
Electronic
Foundation Frontier. September 2009.
9. New Cookie Technologies: Harder to See and Remove, Widely Used
to Track You by Seth Schoen. Electronic
Foundation Frontier. September 2009.
10. Clickstream Raises Questions About Online Privacy by 'Jeff'.
Digital
Business Solutions Blog. February 2010.
11. The Singular Challenges of ISP use of Deep Packet Inspection
by Alissa Cooper. DeepPacketInspection.
Various short articles and links.
12. NCPS under attack over BT and Phorm's covert online monitoring
by Josh Halliday. Guardian.
April 2011.
13. Trusted
Computing Group. Non-profit organization promoting various security
solutions.
14. Why is email address harvesting a bad idea? Bt©B.
June 2007. Illegal in many countries.
15. Privacy.
Daily news, information, and initiatives on privacy issues.
16. Internet Marketing Ethics and Web Ethical Issues: Importance
of Ethics on The Internet. PWebs.
2011. Promotional but useful.
17. Computer Ethics, Laws, Privacy Issues. George
Mason University. Listing of papers and legal provisions by Virginia
Montecino. November 2009.
18. Internet Privacy Law by Timothy. Walton. NetAtty.
2000. Provisions, citations and cases to 2000.
19. Selected State Laws Related to Internet Privacy. National
Conference of State Legislatures. March 2011.
20. Epiq. Email
and online newsletter on civil liberties in the information age.
21. Fact Sheet 18: Online Privacy: Using the Internet Safely.
Privacy
Rights Clearinghouse. August 2011.
22. Privacy
International. A European perspective and beyond.
23. How Privacy Vanishes Online by Steve Lohr. NYT.
March 2010.
24. Protecting Consumer Privacy in an Era of Rapid Change. FTC.
December 2010.
25. Internet Privacy. Encyclopedia
of Everyday Law. Useful summary, with relevant organizations.
26. Electronic Foundation Frontier. EFF.
Defends free speech, privacy, innovation, and consumer rights.
27. Web Tracking and Online Privacy. American
Civil Liberties Union. March 2011. News and articles.
28. E-Scams and Warnings. FBI.
Horror stories and advice.
29. Privacy and Security. Federal
Trade Commission. Detailed advice.
30. Fight Terror With YouTube by Danial Kimmage. NYT.
June 2008
31. Does Privacy Matter? by Joshua Allen. Channel
9. July 2008.
32. The Web of Deceit: Britain's Real Role in the World by Mark
Curtis. Vintage. 2003.
33. Torture and the Twilight of Empire: From Algiers to Baghdad
by Marnia Lazreg. Princeton Univ. Press. December 2007.
34. The Attack on the Liberty: The Untold Story of Israel's Deadly
1967 Assault on a US Spy Ship by James Scott. Simon & Schuster.
July 2010.
35. Operation Northwoods: US Planned Fake Terror Attack on Citizens
to Create Support for Cuban War. What
Really Happened. From Body of Secrets by James Bamford. Doubleday
2001.
36. Press freedom in Russia remains strongly suppressed — survey.
Rianovosti.
April 2004.
37. China Human Rights. Amnesty
International. Articles and stories as they break.
38. Surveillance
and Democracy by Kevin D. Haggerty and Minas Samatas (Eds.)
Routledge-Cavendish. July 2010.
39. Legal aspects of computing. Wikipedia.
40. Privacy. USLegal.
Overview, with links to specifics.
41. List of Whistleblowers. Wikipedia. Listing with outcomes,
many favorable.
42. Whistleblowers:
Broken Lives and Organizational Power by C. Fred Alford. Cornell
Univ. Press. February 2002.
43. 10 arguments for and against WikiLeaks by Jaime Henriquez.
TechRepublic.
April 2011.
44. Catastrophic Failure: UK Loses Records of 25 Million Citizens
by Jason Mick. DailyTech.
November 2007.
45. Prison
Planet. Alex Jones' crusade against government control.
46. Britain's 9-11 Cover-Up: What Will Become of Us? Kevin
Boyle Blogspot. May 2011.
47. Capitalist
Magazine. Many articles arguing for a more 'hands off' approach
by government.
48. House Committee Approves US Internet Spy Bill: This Week in Online
Tyranny by Curt Hopkins. ReadWriteWeb.
August 2011.
49. Spying on First Amendment Activity — State-by-State.
American
Civil Liberties Union. September 2011.
50. Bugger Off: Spying Online Is Perilous and Unnecessary. Review
of Susan Landau's Surveillance or Security? The Risks Posed by New
Wiretapping Technologies by Evgeny Morozov. Boston
Review. September / October 2011.
51. Tracking File Found in iPhones by Nick Bilton. NYT.
April 2011.
52. Web Bugs Can Make Your Privacy Sick by Jim Rapoza. eWeek.
June 2009.
53. Every Breath You Take, Every Move You Make — 14 New Ways
That the Government Is Watching You. Lew
Rockwell. November 2011.
54. Watching Over You: The Perils of Deep Packet
Inspection by Antoine Champagne. Counter
Punch. March 2012.
55. Blowback: The Costs and Consequences of American Empire by
Chalmers Johnson. Metropolitan Books/Henry Holt. 2004.
56. Statistics on Gross Domestic Product (GDP) Correlations.
Filip
Spagnoli's blog. 2008.
57. Bill Summary & Status 112th Congress (2011 - 2012) H.R.3523.
Library
of Congress. May 2012.
58. NSA slides explain the PRISM data-collection program. Washington
Post. June 2013.
59. Where did the Towers Go? by Judy Wood. The New Investigation,
2010. A detailed inventory of 9/11 destruction that goes beyond the
contrary arguments presented in the Debunking
9/11 Conspiracy site to show the official account is false, indeed
impossible.
60. 9/11 Truth Movement. 9/11Truth.org.
Controlled explosion theories: regarded by Wood's supporters as a government-sanctioned
'misinformation' site.
61. The Terror Conspiracy Revisited by Jim Marrs. Disinformation
Books, 2011. One of several books presenting unpalatable but persuasive
evidence that 9/11 was an 'inside job'. (Students should note that
departures from the official 9/11 line are often taboo in college studies,
and may be heavily penalized. Check first with course tutors.)
62. Why Societies Need Dissent (Oliver Wendell Holmes Lectures)
by Cass R. Sunstein. Harvard University Press, 2005.
63. NSA Spying and the Fourth Amendment Snowdenĺs Constitution, Obamaĺs
Constitution, and Criminal Law by Rob Hager.
Counterpunch. June, 2013.
64. Government Spying: Why You Can't 'Just Trust Us' Read more: Government
Spying: Why You Can't 'Just Trust Us' by Marcey Wheeler. The
Nation. June, 2013.
65. Top Secret America: The Rise of the New American Security State
by Dana Priest and William M. Arkin. Little, Brown and Co., 2011.
66. Eavesdropping on the Planet, Whistleblowers and Edward Snowden
by William Blum. Global
Research. June, 2013.
67. Opt out of PRISM, the NSAĺs global data surveillance program.
Prism-Break. July,
2013. A good listing of alternatives.
68. The Breakdown of The Rule of Law: Americaĺs Descent Into Authoritarianism
by Devon DB. Global
Research. July, 2013.
69. NSA revelations over the last month. GCSideBlog.
Guardian corresponent's listing. July 2013.
70. NSA Spying Directly Harms Internet Companies, Silicon Valley,
California ů And the Entire U.S. Economy. Washington's
Blog. August 2013.
71 With friends like these . . .by Tom Hodgkinson. Guardian.
January 2008. CIA investment in PayPal and Facebook.
72. NSA Whistleblower: NSA Spying On ľ and Blackmailing ľ Top Government
Officials and Military Officers. WashingtonsBlog.
October 2013.
73. NSA Spying Directly Harms Internet Companies, Silicon Valley,
California ů And the Entire U.S. Economy. WashingtonsBlog.
July 2013.
74. Spooky Business: Corporate Espionage Against Non-Profit Organisations
by Gary Ruskin. Corporate
Policy. November, 2013.
75, Inside TAO: Documents Reveal Top NSA Hacking Unit by Spiegal
Staff. Der
Spiegal. December, 2013.
76. Tomgram: Engelhardt, The National Security Complex and You
by Tom Engelhardt. TomDespatch.
July, 2012.